Can wireshark display custom options from enhance packet block.
Hi,
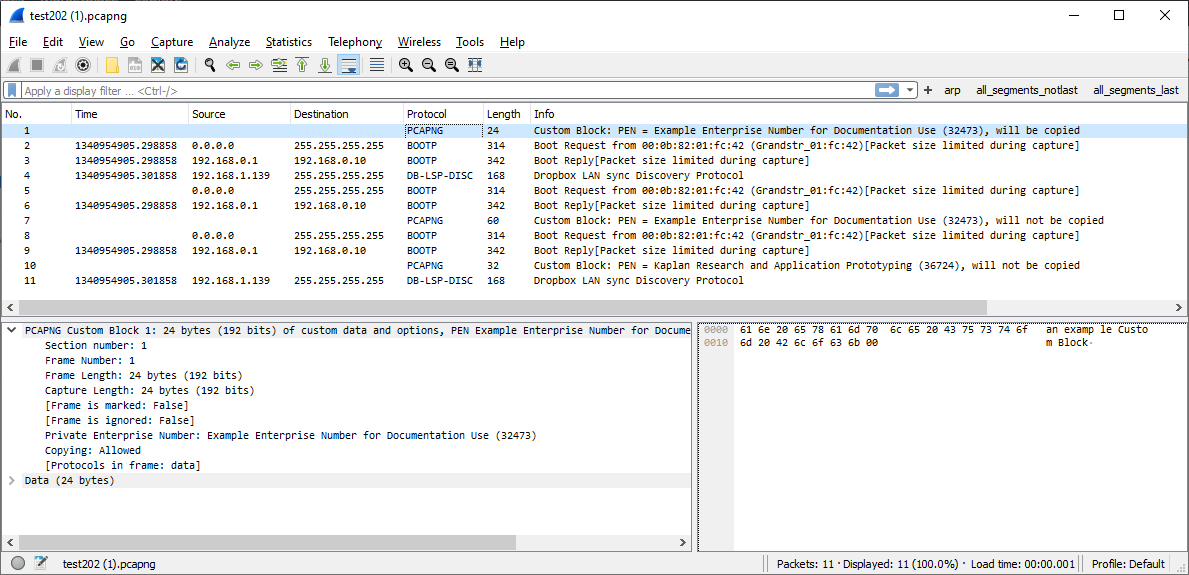
I have a use case where custom options will be added to each EPB in a pcapng file.
Wireshark version 4.0.1 will display a comment option add to the block i.e. code = 1, but nothing is displayed when I use any of the custom option codes 2988/2989/19372/19373.
I am new to dissectors but could not find any way to add logic (via dissector or other) to allow the custom options to be parsed and displayed.
Maybe I have missed something obvious here.
Does wireshark support displaying custom options in a EPB out of the box?
If not, is there a plugin I can write to allow my custom option to be displayed, and more importantly, part of a filter, like the comment option can be.
Thanks in advance.
Dave.