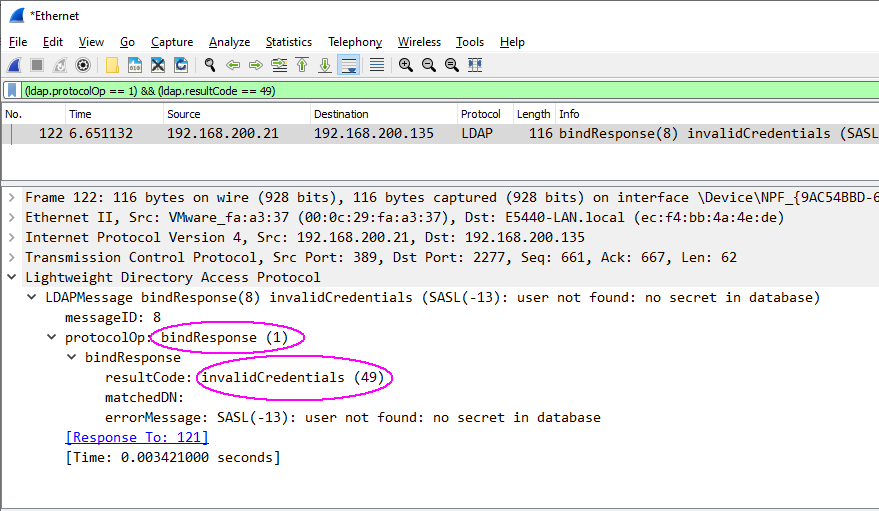
Wireshark - Filter ldap bindresponse with invalidCredentials
Folks,
I am looking for a filter in the Wireshark that allows me to filter the ldap.bindResponse_element containing a message "invalidCredentials".
Thanks in advance.
TM